Torture is a horrific topic and most minds will turn away from it because it can’t be comprehended that humans can be motivated, or computer programs can be run to do this to other sentient beings. Just when we believed we were becoming more civilized as a culture, the technology for torture has advanced more than a hundred fold in recent decades.
This summary will get into ‘the minds of the dishonorable monsters’ of the psychology of torture. Those like Dick Cheney who helped authorize it under certain administrations and regimes of the U.S. government which have been proven to be criminal under U.S. law, treaties, and the International Criminal Court. There are many people involved in the conspiracy and cover-up including General Hayden.
The full report discloses the spectrum of techniques of interrogation and torture used by the U.S. and its allies. The United States government will officially deny the claims of this “no-touch torture report” but in time it will stand firm.
This report will not use skewed, misleading language such as “enhanced interrogation” to describe the torture techniques.
Why torture? The CIA claims it works. The assumption is that it works to gain actionable intelligence. Torture is often used for revenge, punishment, interrogation, and behavior modification. In other terms torture is used to remove the continuity of thought to confuse the target to reveal information, erase brain patterns such as values and beliefs, or to break down the human spirit to make them submit and obey their handlers.
The downside of torture is that the countries that do it lose “moral soft power” in world politics. Without due process, over 25% of those reported in the Senate Torture Report were declared innocent. Blowback is always a repercussion of torture. Torture often takes a long time to affect the target from months to years. Torture has shown to be unreliable except for getting false confessions and bad information but the U.S. and its allies are improving on their tactics and techniques.
The purpose of this report is to draw the parallels between physical torture techniques and no-touch torture methods used in secret by governments who possess the technologies that still go on today. This is a brief summary of offensive psychological and information warfare methods using traditional methods and modern cybernetic techniques while exploring hyper-game theory to walk the target to the desired path: leak intelligence, commit assassinations, or change beliefs.
Numerated Torture Methods for Interrogation and Behavior Modification
(A comparison between physical and no-touch torture tactics)
1. Induction of Depressive/Manic states
The idea is to shake up the emotional states of the target because different information can be accessed at each state. Making the target feel despair and helplessness is the objective. This cycle of hope building and then breaking is done in many ways. The techniques between the physical methods and the no-touch technological methods are similar. Speech is very important during this process of emotional manipulation. Such examples are, “We have imprisoned you without due processes or hope of it. You are indefinitely detained.” Hope building examples include, “Sorry. We have mistaken you for someone else. You will be compensated for false imprisonment and torture.” The main difference between the cybernetic technology and physical is that emotional state clusters can be entrained into the target mind which speeds up the process. The communication is done differently but perceived as human speech. In the no-touch torture methods it is helpful if the target is labeled with mental illness that is being created for discrediting purposes so as not to draw human rights groups’ attention.
2. Memory Erasure
The military and CIA have been researching memory erasing drugs for half a century. The focus of this summary report is on interrogation. Memory erasure is an important technique during interrogation. It is used in combination with sleep deprivation. There are many drugs that have been developed for physical memory erasure. One such interrogation method requires acquiring information from the target while on these drugs and recording the subject. After a sleeping cycle, the interrogator claims that the target has confessed. Of course the target remembers nothing of their conversation. The interrogator will play samples of the subject’s conversation back to them making the subject believe that the interrogator knows more than they do. Similar techniques are used in the wireless, no-touch torture and interrogation programs. The cybernetic methods of memory erasure have additional purposes. The memory erasure can be used on the cybernetic target to make the target believe people have broken in and moved their belongings. While physical black bag jobs do occur, it is a way to make the target more paranoid.
3. Electricity and Shocks
Pain and fear of death are common tactics during interrogation. Shocking by electricity is a traditional method of torture and exposed in the CIA’s secret prisons. Shocking the testicles and nipples are the most common due to their sensitivity. Interestingly, the thousand of interviews of no-touch torture involves “stings” and “shocks” to various parts of their bodies over long durations.
4. Fear and Terror
There are many techniques to induce extreme fear in the target. In physical renditions dogs, power drills, guns, insects, mutilation, blow torches, water boarding, suffocation, mock burials, and mock executions are just a few the United States government have used. Remember that many targets of torture die from the physical effects. It is torture to death.
Let us compare the no-touch torture methods used to inflict the same terror and mental anguish. In several of these techniques the target needs to hear their handler’s voice. This report does not describe the technologies used to broadcast voices to the target at a distance. While the subject can be broadcast mental images to their mind using hypnosis and other suggestions as well as visual entrainments, the more invasive controls of the brain manipulation technologies can be used to entrained the brain’s autonomic nervous systems such as not breathing causing the target to not be able to sleep from fear of suffocation equivalent to water boarding. The neural linguistic programming can add fears such as heart attack, stroke, and cancer threats.
Even motor cortex mapping can cause twitches in any part of the body. One example used a swift neck movement with a voice transmission, “We are trying to break your neck.” Directed energy effects such as Active Denial System can make the target feel that they are on fire indefinitely without the target dying from burns. Maximum pain and torture weapons have been evolving. Every drug effect can be artificially induced into the target mind including those of poisons.
5. Imprisonment and Isolation
Isolation is commonly used as punishment in prisons. Many whistleblowers like Bradley Manning suffer this condition. In soft interrogation it is used to get the target to talk to their interrogator since humans have the need for companionship. In no-touch torture the target is driven from their friends and family using different techniques in order to isolate them so that the electronic mind control has more effect on their psyche.
Like in Guantanamo, the target becomes isolated losing their job and medical care. Part of the method involves slander in their community. They end up on the most part in poverty and paranoid about doctors and other people from false correlations that are purposefully induced into their lives. Isolation is also a form of sensory deprivation which will be discussed later. Days and weeks lose their meaning.
6. Sexually Disturbing Tailored Pornography
The Summary of the Senate Torture Report disclosed the disgusting revelations that in the secret torture prisons the targets were forced to perform homosexual acts on each other against their will and religion in order not to be beaten or killed. This is a common break down tactic of belief systems and the human will. In no-touch torture the techniques are more psychologically specialized for each target. Most common examples include homosexual targets that are forced with voices that are derogatory to their lifestyle and similar mental images. Almost all targets are forced to view child pornography in their minds. And vice versa is true, that heterosexual targets are forced to view homosexual sexual acts like in the secret U.S. torture prisons.
7. Mutilation
Also mentioned in the declassified report on torture was mutilation of the human. Cutting the naked target’s penis and scrotum, pulling nails or teeth is common. In no-touch torture mutilation is done by trickery. Let us look at a couple examples. There have been several targets who believed that the microwave hearing effect and other voice induction methods were done by microchips implanted in their teeth or ears. They had all their teeth pulled because they believed it was a technology called bone conductance. Others have poked out their ear drums in the belief they had micro implants in their ears. There are many more examples of trickery used to make the targets mutilate themselves
8. Personal and Spiritual Defamation
In physical torture the CIA and other groups use propaganda and defamation of character for those they oppose. For detainees they try to disenfranchise the target from their religion. They will defecate on their Bible or Koran for example. They might say, “Why is your God not saving you?” In no touch torture and behavior modification they might try to make an atheist believe in god. It is just a mechanism to alter belief systems for control and experimentation. Perhaps the target may wish to confess their secrets to a “voice of god weapon”. Information warfare covers the gamut of electronic communication as well. The government training exercise uses language like “befriend”, “infiltrate”, “mask/mimic”, “ruse”, “set-up”, “disrupt”, “create cognitive stress”, “use deception”, “ruin business relationships”, and “post negative information on appropriate forums” in a malicious effort to target bloggers, activists, journalists, social event organizers and anyone else deemed to be a ‘emerging leader’ or voice in the public sphere.
9. Psychological Intimidation
This is a topic for a target at the beginning of the trials and programs. Physical break-ins are common even if the target has an alarm system. The NSA has used stalking of foreign officials in the past for economic gain. The FBI does black bag jobs to invade a home without a warrant. The point is to let the target know they are being watched and to increase their paranoia. The NSA easily hacks all computer systems and causes harm to the victim’s intellectual property and their relationships from that endpoint. In the no touch torture false correlations between pain and a neighbor coming home can be induced.
10. Rape
Rape is a common practice in torture. It causes much psychological trauma. In the United States methods of rape in their military and CIA secret prisons it is often relabeled. It is commonly done by prods but “rectal rehydration” is the more common misnomer. Often they call it forced feeding through the rectum but it is meant to induce psychological scaring and trauma. Several have died from the technique due to rectal bleeding. In no-touch torture the psychological trauma of simulated rape takes on different forms. Using technique often called EEG-heterodyning the targets will receive molestation effects of their genitals. In men this can be the anus and genitals. Similarly women can be wirelessly raped by the analogous function of perception.
11. Dietary Manipulation, Forced Weakness and Sickness
The idea behind dietary manipulation is to weaken the target. This is easily done in a physical setting but in no-touch the hunger trigger needs to be suppressed. Sometimes a false correlation between eating food and sickness is induced to make the target believe they are being poisoned. However, poisoning is common in physical renditions too.
12. Repetition
Verbal breakdown is most important during interrogations and torture. Obviously speaking the language of the target is necessary. This is why there are interrogators in all languages. Repetition is an important neural linguistic programming interrogation tactic to influence the target mind. During the breakdown process, threats to kill and to torture the target’s family or friends are common. Repetitious questioning and breakdown phrases are automated in both the physical and no-touch versions of torture. An interesting technology that is used for no-touch torture is called chatter bots. Chatter bots, an artificial intelligence program, automate much of the repetition so that the interrogators don’t drive themselves crazy during the neural linguistic torture and programming phases. Let us not forget the Chinese Water Torture, a single drop of water on the forehead of the detainee for months. Repetition is a form of torture.
13. Sensitization of Pain Impulses
While the reverse can be obtained, optimizing perceived pain and misery is the objective in torture. Each trauma adds to the overall misery throughout life. Optimization of pain has been studied by the military and intelligence agencies. In the past the CIA has used drugs such as LSD to enhance fear and terror in the subject. Other methods such as hypnosis can increase perceived pain and the power of suggestion such as telling the subject his pinky finger is going to be cut off before it is done. In no-touch torture the same psychological manipulations are exerted. Subliminal and overt suggested are often told to the subject before the directed energy or EEG heterodyning pain inductions in order to maximize their effectiveness.
14. Sensory Overload and Deprivation
Again, this technique of overloading or depriving the human of sensory stimulus is ubiquitous in torture around the world not just in U.S. secret prisons. Torture subjects in the United States have reported the use of repetitive bad music and noise campaigns. An unusual torture technique used in the U.S. secret prisons was of a use of a plastic suit filled with ice while they beat the target. Ultra bright lights for days on end in the prison and hot/cold temperature changes in the environment are frequent. In no-touch torture, the target’s brain is forced to release dopamine which causes pupil dilatation. This acts as a sensory overload. For example the non-lethal microwave weapons research done by a professor in University of Nevada has shown this capability. Body metabolism can be altered with these weapons causing cold and hot flashes. Targets of no-touch torture often hear endless tinnitus.
15. Sexual Humiliation and Lack of Privacy
Often used in common prisons is a lack of privacy. It is both necessity for security and a form of sexual humiliation. Also in prison many people are raped. No-touch torture offers the same sexual humiliation and lack of privacy by using through wall radar, cameras, and EEG visual cloning to let the target know they are being watched. Degrading comments are often used on the no-touch torture subjects while they are naked or in the bathroom.
16. Maximum Sensory Pain Techniques
Basic torture involves brutalization, i.e. physical strikes, kicks in the groin, pepper spray or tear gas, etc. Anything that involves maximum pain is the objective. Amazingly, these same basic tortures can be done wirelessly into the human mind. All forms of sickness have been reported without any real illness behind the suffering. All suffering can be entrained into the minds of no-touch torture subjects.
17. Sleep Deprivation
This is the number one torture method along with the popularity in the press of water boarding. This is done in every country that uses torture. The United States is number one in torture since they are currently the world’s only superpower. A repetitive sleep deprivation cycle is generally done 180 hrs/7.5 days at a time in the physical renditions, or in no-touch torture five days awake and two days of sleep. Sleep deprivation accomplishes the objective of memory loss during interrogation and induces hallucinations which help with the interrogation process. In behavior modification and programming it is necessary too.
18. Stress Positions
Keeping detainees handcuffed above their head and to walls so that they must stand for days is a common ploy in torture. These types of poses are called stress positions. They can be mimicked in no-touch torture. An example of one such trick requires the target to believe they can deflect radar energy using pots or pans and that it is directional. The target is being given an ample amount of pain until their hands and arms are spread apart holding the pans trying to block the signals. They must maintain that position in order to get any relief from the torture signals. However the stress position itself is physical torture. Often accompanying this technique are voices saying to the target, “You are doing it to yourself.”
We will finish off this summary of U.S. and its allies’ torture, interrogation, and behavior modification experimentation with ideas of why they are done to the general public and falsely accused detainees. Anyone can be put into these programs. Justice and rule of law does not exist at the highest levels of government. Treaties are worthless because the #1 agreement in the rules of war, a ban against torture, is not obeyed. This creates a more brutal and barbaric society lead by example.
No-touch torture uses the same interrogation tactics as physical interrogations but with some new twists. Techniques such as “Jeff and Mutt” a.k.a. “Good Cop Bad Cop” are used. The bad cop tortures the target and the good cop tries to gain their trust. In mind control, trust games are commonly employed to manipulate the beliefs of the target. Creating hatred of groups through false correlations and deception is a common CIA method of trickery.
In the CIA programs, the target is put through these phases as written in the documentation, “Disorient and confuse the target. Use them for our purposes, and then dispose of them in any way possible.” We can only surmise by our sample set of a thousand people what “dispose” means: prison, suicide, or perhaps a mental hospital. Coercing and torturing people to suicide is very common. Both tactics in physical or no-touch torture involves plausible deniability.
The no-touch interrogations are better than physical rendition techniques for exposing support networks. Traditional NSA tracking of email and phones calls are useful but if the targets are taken into a secret prison they can’t contact their networks. In no-touch torture, the target will contact everyone who might help them. Then those relationships can be destroyed to isolate the target. All these techniques rely on the target having a fear of death and pain.
Deception is very important during interrogation. In physical interrogations the targets are often drugged. This creates the confusion necessary to pull off certain trickery. In terrorist interrogations, for example, the CIA uses fake newspapers to make the target believe whatever event they were suspected of plotting had already happened, obviously looking for a confession. Sometimes the government in charge of the torture is looking for a political gain through a false confession. None-the-less false flag operations are commonly used in both forms of torture and interrogation. The trick is to make the target believe another foreign country is doing it to them. In no-touch torture the trick is to make them believe someone related to them is behind their suffering.
Voice transformation and morphing is an interesting technology also used in both physical and wireless interrogations. It is a form of deception used against a target to trick them into believing that they are speaking to real people that they know. It has been used in war to trick generals. Obviously spoofing email and other identities on internet forums can be used in this manner too.
Finally, the topic of human experimentation for improving weapons, torture, interrogation, and social disruption methods will be breached. Most of the techniques mentioned above work most effectively if the target has no SERE training (Survival, Evasion, Resistance and Escape) or psychological understanding of the methods to influence the human mind. Unfortunately, every sample point in the world’s society needs to be studied to improve the weapons systems. This is why many random people are put into the torture and mind control experiments. There are some devious uses of a secret army of remote controlled assassins in every country in the world. The samples must include different education, language, culture, and economic factors. Obviously, silencing dissidents, oppositions of political parties, and whistleblowers are included in the lists of applications. The most disturbing of the trends in torture is testing and improving it. No-touch torture is much more complex than physical torture. Testing design flaws and weaknesses of the signal intelligence is one reason why it is necessary to test on innocent targets. Often the subject will be taunted by the statement, “Try to stop us.” This statement forces the torture subject to try to figure out shielding and jamming techniques to stop the wireless torture and helps the weapons designers to improve on the system.
However, the psychological and perceived physical pain is only half the story with no-touch torture. It also involves a set of scripts, mind games if you will, to walk the target to murder and/or suicide. This is called “Hyper Game Theory”. It is used in war games to determine how to control your enemies and targets. Game Theory can be used on governments, individuals, or for determining propaganda to alter cultures. The experiments on the public provide a means to test the efficacy of these scripts and determine under what circumstances to use them.
One last comment on why “We must guard against the acquisition of unwarranted influence, whether sought or unsought, by the military industrial complex” as President Eisenhower warned. During these torture programs run by the United States and its allies, accurate “truth” data points need to be used to judge the efficiency of the interrogation methods. This is why there is a dispute between the CIA and Senate Intelligence Committee reports about the usefulness of torture. Subterfuge by the CIA hacking into the senate oversight committee’s computers is a big deal; a rogue agency has been formed. Data fusion centers, Homeland Security Data Fusion Centers, NSA, and FBI collect data on Americans. This data in turn is used during torture and interrogation of Americans in no-touch torture.



















Video MUST WATCH!!!
You probably wonder why we compare "John's" ex-wife Danielle Debets with "Hillary Clinton" and What about the "Sony Hack" Danielle's Ex Work employee was Sony, And because the AIVD (Dutch NSA) Filmed "John" We have released video on "Sony" Movies (Sony Targets Danielle and AIVD). This will all make sense in the end. At the end of this "Conspiracy" You will understand what Anonymous is and how powerfull our messages truelly are. The upcoming video's where an operation from Anonymoous right from the start. Every single detail will mindfuck your mind. Are you awake? We are Anonymous!
Now look at these facts below:
The Hacking scandal in the Netherlands how NSA lost control and "Wanna-Cry" Ransomware infected a whole country and they blaimed "Russiam Hackers" The shadow brokers. Write the date from the picture below on a paper for the upcoming video's: Fact Number: 1

Update: This video was releassed on 7 July 2017
The Hitman's Chasing "Set Rich". Note the date's: Fact Number: 2

The Hospital Attack on "Set Rich". Note the date's: Fact Number: 3

The Hitman - Sniper Rifle at the day shelter. Note the date's: Fact Number: 4
His Ex-girlfriend who gaved permission to rent a hitman on "Set Rich"(later on this): Fact Number: 5
His Ex-girlfriend as "Hillary Clinton" Who flight to Italy for a business meeting with the FBI in 2016 (True Story)-Brainstorme: Fact Number: 6
The Motorclub House Presented as "The White House" in the movies: Fact Number: 7
Over a Million spended to hunt down and target the individual. think about the cost of months of wiretapping, observation, crime scenes and bribery: Fact Number: 8

Now Watch this Video's below. Compare the dates from the crimes from the pictures above this text and check the dates from the uploads from the following video's. When we posted these video's last year they where taken down several times because of their accuracy. This is "Fake-News" Real News. Have fun watching them. Sponsered by the Truth Factory - Conspiracies on "Set Rich" As you can hear in the last two minutes it's not certain if Set Rich is death or in a witness protection programm. Hi I am Set Rich. Check out my video's and read this article again. Take your time and have fun watching them. We Are Anonymous!


First video on "Set Rich" Case
Mindblowed? Second video:
Oke yes.. I will reveal some secrets about my work later.. It's called a Global Network..(17 Days after the Torture Attack 13th May 2017 on "John" a.k.a. "Set Rich" We released this video. Government shutted down all our accounts where we posted this "Conspiracy" So take attenton!!! (Sorry for the Sponsors in this video, These Sponsors make this work possible so if you mind them skip forward a little bit, thank you for understanding).
This is how you bring real news



"Sony" Or for the people who still don't understand the "Conspiraxy" had filmed "Set Rich" and Blackmailed him so "Hillary Clinton" a.k.a. Danielle Debets released some video material to ruin his reputation. This is called Character Assassination. AIVD Sold Video material to the Hells Angels Who Attacked "Set Rich" Here is The Video from Anonymous to Sony
"The Blackmail"

So what where they looking for, And what did they found? The following image is a conversation between "John" and Danielle Debets. Danielle Debets knew that "John" was a Pedo Hunter:

The image Translated:
John: You have said to Steven that i am a pedophile, You knew my mission and intension to them you knew it goddamn it. (Steven is the son of a Hells Angel Gerrit Ruitenbeek). With him started the discussion about the pedophelia and they started filming John in his house. Nevertheless they couldn't prove John guilty for Child Pornography. Instead of Chilpornography they tried to cover their traces and silence John.) Later about this more.
Danielle: What? What a mongol if he said that, i NEVER said a word wrong about you. I always said i dont want to hear anything from you. (In mather of fact this aint true) because everytime she was looking for John where he was going out and we have released the conversations about "The Rape Train" that was in the same time period. Steven was John's best friend and suddenly Danielle came back in his life and John lost all his friends. Because she was telling everyone John was a Pedophile. (Character Assassination).
So Anonymous and LT.Lick Me made several video's about this scandal
Are you ready?
We Are Anonymous
We Are Legion
United As One
Divided By Zero
We Do NOT Forgive
We Do NOT Forget
Expect Us!
So here is Stephen's Video calling "John" a Pedophile (Another fact Debunked)
Video 2: Message to Hillary Clinton a.k.a Danielle Debets Another Project from Anonymous. The sound track connects with the next video!
And now We present: LT.Lickme Cheating Girlfriend Special!
Same Beats Same Group, Same Anons, ;) We Are Anonymous!

The Next video is an interview with Anonymous about The FBI "ClickBaits" (33 minutes but interresting). This is what they tried on John but didn't succeed. In my next video we will explain what "John's" a.k.a. "Set Rich's" Motives where and why they wanted to kill him.
So now you have seen the motives of the FBI and their tactics time for the next video and the truth about why he was being hunted by NSA/CIA
It's True in 2015 "John" exposed NSA's Childporn hosting network and in 2017 he exposed an russian Childporn network. What about that!!!
After The attack at the Hospital we made an Reconstruction video to awaken people about the ideo about how they can deliver maybe existend evidence, This video is released on 30th May 2017, 17 days after the attack on "John" "Set Rich" This has to tell you something! Yhe video is named Where is the footage, because the Cops took away the Video Evidence. Hi I am Set Rich, and I am under Witness protection my death is a big conspracy to protect my real indendity. Connect the dots and there is no thing like "Fake News" We Are Anonymous: video below:




Still Reporting Last bombshell on the Set Rich Case, another video about the home camera's and the sniper firering. (sorry for the advertising in the video).


The image Translated:
John: You have said to Steven that i am a pedophile, You knew my mission and intension to them you knew it goddamn it. (Steven is the son of a Hells Angel Gerrit Ruitenbeek). With him started the discussion about the pedophelia and they started filming John in his house. Nevertheless they couldn't prove John guilty for Child Pornography. Instead of Chilpornography they tried to cover their traces and silence John.) Later about this more.
Danielle: What? What a mongol if he said that, i NEVER said a word wrong about you. I always said i dont want to hear anything from you. (In mather of fact this aint true) because everytime she was looking for John where he was going out and we have released the conversations about "The Rape Train" that was in the same time period. Steven was John's best friend and suddenly Danielle came back in his life and John lost all his friends. Because she was telling everyone John was a Pedophile. (Character Assassination).
So Anonymous and LT.Lick Me made several video's about this scandal
Are you ready?
We Are Anonymous
We Are Legion
United As One
Divided By Zero
We Do NOT Forgive
We Do NOT Forget
Expect Us!
So here is Stephen's Video calling "John" a Pedophile (Another fact Debunked)
Video 2: Message to Hillary Clinton a.k.a Danielle Debets Another Project from Anonymous. The sound track connects with the next video!
And now We present: LT.Lickme Cheating Girlfriend Special!
Same Beats Same Group, Same Anons, ;) We Are Anonymous!

The Next video is an interview with Anonymous about The FBI "ClickBaits" (33 minutes but interresting). This is what they tried on John but didn't succeed. In my next video we will explain what "John's" a.k.a. "Set Rich's" Motives where and why they wanted to kill him.
So now you have seen the motives of the FBI and their tactics time for the next video and the truth about why he was being hunted by NSA/CIA
It's True in 2015 "John" exposed NSA's Childporn hosting network and in 2017 he exposed an russian Childporn network. What about that!!!
After The attack at the Hospital we made an Reconstruction video to awaken people about the ideo about how they can deliver maybe existend evidence, This video is released on 30th May 2017, 17 days after the attack on "John" "Set Rich" This has to tell you something! Yhe video is named Where is the footage, because the Cops took away the Video Evidence. Hi I am Set Rich, and I am under Witness protection my death is a big conspracy to protect my real indendity. Connect the dots and there is no thing like "Fake News" We Are Anonymous: video below:

































Message to "Sony Operation PayBack"
Message From Anonymous #OpPapaparazi
The Man Behind The Mask











































































































#OpIcarus 2018 Engaged





#Operation PayBack 2018 By Anonymous Netherlands
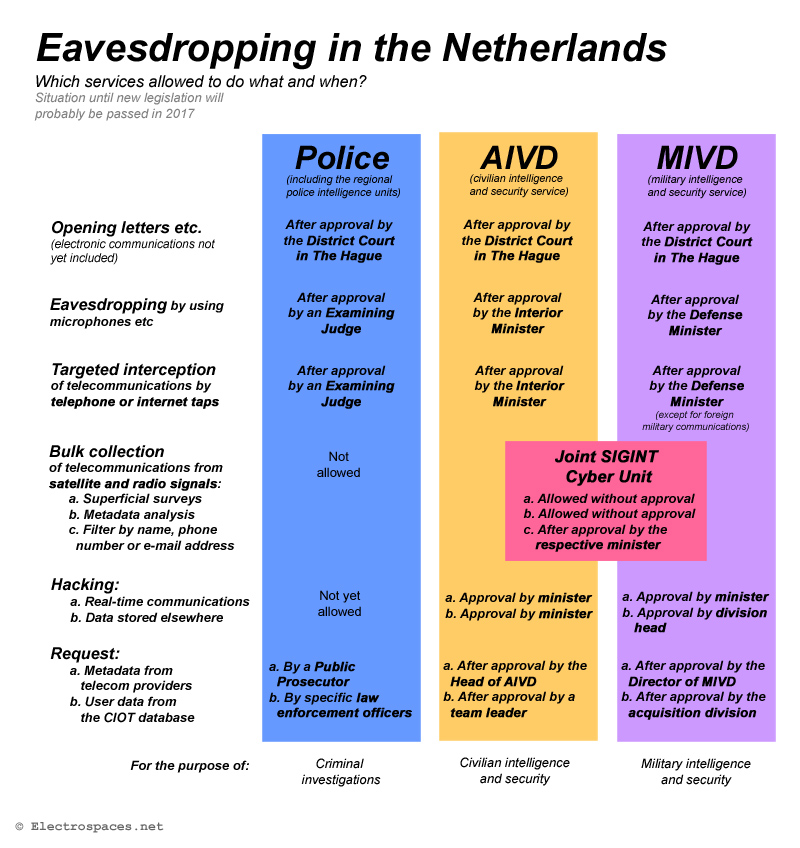
Website Updated with new content: Complete Dutch NSA program named AIVD and MIVD and the laws and human rights in the Netherlands. and Scroll down to the bottom of this webpage for a complete overview from the shortcuts used by the NSA Operations. #OpNSA Engaged. Complete NSA Program exposed by Anonymous Ghost Security Team Europe. Expect us for more. We also uploaded the Top secret Documents from the NSA - AIVD SIGINT program. (Targeted Hacking by government)


#Operation Expose #Gangstalking #Engaged #Operation Matrix #Engaged
#Intel Group Release the Information!!!




The Threathening Messages from May 2017 from Danielle Debets to John The Targeted Individual








This is Danielle Debets she plets guilty on Gangstalking activities and Threathening to rape her ex-boyfriend, after the threatments made by Danielle, John got tortured by Hells Angels and Cops, The police database numbers of the dates and place when it happened are on the bottom of this webpage. The video evidence is taken away by the police this whole incident happened under video surveillance from the Hospital Atrium MC Heerlen City The Netherlands.
Name first Gangstalker: Danielle Debets.
Country: Netherlands.
Adress: Kip straat 51 6461 GV City Kerkrade
Birthday: 23 February 1990
Social Media accounts:
facebook:https://www.facebook.com/profile.php?id=100005085045737
Instagram:https://www.instagram.com/dnielle___/
Workingplace: Q-Park Maastricht
Danielle Debets We Give You one chance to go the Police and tell them the truth about your lies about the rape claims and about your treaths to Rape "John". In trade for Honesty and Justice we will take of your personal details from this website. be warned we have alot more intel gathered. and this is a warning for other involved Gangstalkers to. You are next! As You can read in the articles below on this website the NSA has the possibilities to trace back all evidence. So Government of the Netherlands it's now your duty to do your homework. As it seems that the things written on facebook messenger are stored on a database can't be deleted. this girl goes guilty as HELL. So tell me who are the real criminals here? is it legal to threat people with rape and bribe police and let them torture by Outlaws? Just wait for it we will post more soon. We Are ANONYMOUS. WE DO NOT FORGIVE. WE DO NOT FORGET. EXPECT US!!!





Dutch government tried to hide the truth about metadata collection
On February 4, the Dutch government admitted that it was not NSA that collected 1,8 million metadata from phone calls of Dutch citizens, but actually their own military intelligence service MIVD. They gathered those data from foreign communications and subsequently shared them with partner agencies like NSA.
Just like everyone else, the Dutch interior minister was mislead by how Glenn Greenwald erroneously interpreted the data shown in screenshots from the NSA tool BOUNDLESSINFORMANT. This let him misinform the Dutch public and parliament too, and only after being faced with a lawsuit, he finally disclosed the truth. Here's the full story.
How it started
The first charts from the BOUNDLESSINFORMANT tool were published by the German magazine Der Spiegel on July 29, 2013. Next to a bigger chart about Germany was a smaller one about the Netherlands, but this was completely overseen by Dutch media.
Only after the French paper Le Monde came with a big story about alleged NSA eavesdropping on French citizens on October 20, 2013, the Dutch IT website Tweakers.net published on October 21 about the screenshot that was in Der Spiegel several months before:
The report by Tweakers.net was correct in explaining that the chart only shows metadata, but the headline initially read "NSA intercepted 1.8 million phonecalls in the Netherlands". It was the first time a news medium correctly presented the BOUNDLESSINFORMANT chart as showing metadata instead of content.
But as the initial headline had immediatly been copied by other media, many people, including politicians, got the idea that NSA was actually eavesdropping on a vast number of Dutch phone calls. After discussing this on Twitter, Tweakers corrected the title by adding "metadata" and "per month".
> See also: BOUNDLESSINFORMANT only shows metadata
A talkative minister
On the night of October 22, the Dutch interior minister Ronald Plasterk was asked about these revelations in the late night talk show Pauw & Witteman. He gave a clear explanation about what metadata are used for, and guessed that with around 60.000 phone calls per day between the Netherlands and the United States, this would make 1,8 million calls per month - apperently assuming that numbers of metadata equals phone calls.
He said that he wasn't yet certain whether it was actually NSA that collected those metadata from Dutch phonecalls, but that a European group of experts was established to clarify this with the Americans. The minister said that it would not be acceptable if NSA was monitoring Dutch citizens without asking permission from the Dutch government before doing so.
According to a statement by the interior minister during the parliamentary debate on February 11, 2014, it was only by now that AIVD and MIVD started communicating with NSA about the exact origins of these particular data. It would last 4 weeks to get this clear - rather quick, according to the minister.
Before this bilateral investigation was initiated, it seems that the Dutch government was relying on the work of a multinational group of experts on behalf of 27 European countries. This ad hoc EU-US Working Group was established in July 2013 to examine the NSA spying programs. Their final report (pdf) was published on November 27.
Besides this group of experts, the Committee on Civil Liberties, Justice and Home Affairs of the European Parliament also started an inquiry in September 2013, presented preliminary conclusions on December 18 and a final report (pdf) on February 21.
(October 22, 2013 - in Dutch)
Almost one week later, on October 28, the Spanish paper El Mundo also published a screenshot from BOUNDLESSINFORMANT. The article, written by Glenn Greenwald and a Spanish journalist, once again said the chart proved that NSA had spied on 60 million phonecalls from Spain in one month.
This was the standard interpretation that Greenwald gave to BOUNDLESSINFORMANT charts for Germany, France, Spain, Norway, Afghanistan and Italy. He used them to demonstrate the claim made by Edward Snowden, that NSA is eavesdropping on innocent people everywhere in the world.
By framing the public debate in this way, most people, including politicians, assumed these claims were true, and therefore it was for example the Dutch interior minister, responsible for the civilian intelligence and security service AIVD, who was asked for explanation. Only people familiar with Dutch intelligence knew that SIGINT collection is actually done by the NSO, which is part of the military intelligence agency MIVD.
NSA strikes back
On October 29, NSA director Keith Alexander testified before a hearing of the House intelligence committee. He forcefully denied that NSA was collecting millions of phone calls from European countries by saying "Those screenshots that show or at least lead people to believe that we, NSA, or the US, collected that information is false".
Instead, data shown in charts from the Snowden document were collected not just by the NSA itself, but were also "provided to NSA by foreign partners," Alexander said. "This is not information that we collected on European citizens. It represents information that we and our NATO allies have collected in defense of our countries and in support of military operations". The next day, this statement was also sent to European partner agencies, including AIVD.
The same day, the Wall Street Journal reported that according to US officials, the metadata records for France and Spain were not collected by the NSA, but by French and Spanish intelligence services. The metadata were gathered outside their borders, like in war zones, and then shared with NSA.
Then, interior minister Plasterk was invited to appear in the Dutch television news magazine Nieuwsuur on October 30. According to a reconstruction by the newspaper NRC Handelsblad, he was advised by Defense minister Hennis-Plasschaert not to go, because her department, responsible for Dutch SIGINT collection through the MIVD, was irritated by Plasterk's willingness to talk about this issue.
Before going to Nieuwsuur, Plasterk had a meeting with Marc Kuipers, the deputy director of his own AIVD and asked him about the metadata. He was told that there was no hard evidence that the statement of NSA was correct, and Kuipers reportedly denied that the 1,8 million metadata were collected by Dutch agencies. As their research started just a week before, AIVD apparently wasn't sure yet about the exact origins of these data (it took the German BND only a week to find out that they collected the 'German' metadata *)
During the Nieuwsuur broadcast, minister Plasterk showed the letter (pdf) with the statement from general Alexander, but completely misinterpreted it as being a confirmation that the number of 1,8 million metadata were actually collected by NSA - something that was not acceptable for him. He also strongly denied that the 1,8 million were collected by Dutch agencies and subsequently shared with NSA.
A few weeks later, NRC Handelsblad announced that they would soon start disclosing Snowden documents related to the Netherlands. NSA watchers expected that one of the first disclosures would be the complete BOUNDLESSINFORMANT screenshot, including the bottom part showing the technical specifications. But that didn't happen. NRC published two articles, on November 23 and November 30, but both contained more background information than spectacular new revelations about the Netherlands.
Most surprising was that the BOUNDLESSINFORMANT screenshot wasn't published. Maybe it had something to do with the fact that this weblog explained on November 23, that Greenwald's interpretation of these charts was not correct, which became clear after comparing two screenshots published by Greenwald in a Norwegian paper in the days before.
A few days later, on November 27, I published my research revealing that the DRTBox technique used to collect the metadata shown in the charts about France, Spain, Italy, Norway and Afghanistan is mainly used for short-range radio and cell phone interception during military operations.
Not NSA, but MIVD
These analysis not only support the official statement by NSA, but also confirm what the intelligence agencies from Germany and Norway had said earlier: that the metadata shown in the charts were collected by them as part of military operations abroad, and not by NSA (exactly the same was said by the Danish military intelligence service, anticipating on a chart about Denmark that never came).
After an investigation of exactly 4 weeks, experts from AIVD and MIVD, who compared actual data collected by the SIGINT unit NSO with data in the systems of their counterparts from NSA, concluded that there was a "perfect match". This was shared with defense minister Hennis and interior minister Plasterk on November 22. Prime minister Mark Rutte was informed during a regular meeting on December 10.
After it became clear that the metadata were not collected by NSA, but by the Dutch agency MIVD, the whole issue automatically became something that was not in the interest of the state to disclose (although not a formal state secret). The interior and the defense minister argued about whether to inform parliament and the public, like in Germany and Norway, but ultimately decided not to do so, following the standard practice to Never Say Anything about the modus operandi of the intelligence and security services.
This is a rather strange argumentation, as "collecting and sharing (meta)data" doesn't reveal any specific methods or operations. Both practices are regularly mentioned in the public reports of MIVD and the oversight committee CTIVD. But as almost no one reads these, the parliament and the people still thought it was NSA that monitored their phone calls.
Presently, it's still not clear whether or not the government informed the parliamentary intelligence oversight committee (CIVD or Commissie Stiekem), because ministers and members aren't even allowed to mention which topics were discussed during the committee meetings.
Update #1:
According to an article from February 18, 2014 by NRC Handelsblad, defense minister Hennis and the head of MIVD informed the parliamentary oversight committee on December 12, 2013 by saying that the telephony data were collected by Dutch services and shared with NSA. Apparently, this wasn't linked to minister Plasterk's statement from October 30, so most of the committee members weren't aware of the political impact.
Update #2:
In November 2015, it came out that already on March 13, 2014, the chairman of the CIVD had asked for a police investigation into which member leaked to NRC that the committee had actually been informed. As the police isn't authorised to charge members of parliament, they handed over the case to the presiding committee of the Lower House of Parliament, which started its own investigation into the leak on November 12, 2015.

Members of the intelligence oversight committee CIVD or Commissie Stiekem
leaving the conference room after a meeting on February 18, 2014
(still from the Nieuwsuur TV magazine)
Citizens against the State
But then there was a lawsuit on behalf of a coalition of citizens and organizations against the Dutch state, as represented by the interior minister. It aims at stopping Dutch intelligence agencies acquiring data from NSA that might be obtained illegally if Dutch and European law would apply. Furthermore, the coalition demands that the state informs the citizens whose illegally obtained data have been used.
Faced with the possibility of a court ruling that acquiring foreign intelligence might be illegal, which would de facto end the intelligence sharing relationships with foreign countries, the Dutch government was forced to reply. So on February 4, 2014, the state advocate came with a response (pdf), which contains two interesting points:
- The demands are mainly based upon press reports speaking of intercepted phone calls, which is incorrect, because in fact it's not about content, but about metadata. These are collected by the state, lawfully acquired in the context of international cooperation and subsequently passed on to other countries. (par. 6.2)
- Dutch intelligence services are using data derived from undirected interception of cablebound communications by foreign agencies. This method is (still) prohibited in the Netherlands, but legal in the US, and therefore the state sees this as lawful acquisitions. (par. 2.17 - revealing that this is apparently one of the things that the Dutch get in return for the metadata they share)
Misleading the parliament
Now that the state advocate had disclosed the true nature of the 1,8 million, the interior and the defense minister also had to inform the parliament and the public. This was done by a short official statement saying:
"The graph in question points out circa 1.8 million records of metadata that have been collected by the National Sigint Organization (NSO) in the context of counter-terrorism and military operations abroad. It is therefore expressly data collected in the context of statutory duties. The data are legitimately shared with the United States in the light of international cooperation on the issues mentioned above."
This was exact the opposite of what interior minister Plasterk had said during the Nieuwsuur broadcast on October 30 and subsequently to parliament. He was accused of lying or at least witholding crucial information and now had to fear for his position.
On Saturday, February 8, the newspaper NRC Handelsblad published out of the blue the long-awaited complete BOUNDLESSINFORMANT screenshot regarding the Netherlands, including the bottom part which was seen now for the first time since the initial publication by Der Spiegel in August 2013:

The BOUNDLESSINFORMANT screenshot for the Netherlands
(picture by NRC Handelsblad - click to enlarge)
> See for all details about this chart: BOUNDLESSINFORMANT: metadata collection by Dutch MIVD instead of NSA
On February 11, there was a parliamentary debate about the whole issue. Interior minister Plasterk sincerely apologized for his misleading statements on October 30, saying that he just wanted to make sure to the public that it was not his own AIVD that eavesdropped on Dutch citizens.
This statement was hardly convincing, and many parliament members were not satisfied with the fact that he didn't correct his statement after he was informed about the truth on November 22. Both the interior and the defense minister continuously replied that it was not in the interest of the state to provide any more information.
Given this overstretched secrecy, it almost seemed a slip of the tongue when minister Plasterk explained that because "under different programs, different types of metadata are shared" it was not so easy to attribute the 1,8 million to collection by MIVD.
After a debate of almost 8 hours, most opposition parties voted against the interior minister, but that wasn't enough to force a resignation. However, the whole affair weakened his position, he can't afford new mistakes anymore.
Conclusion
With claims made by Edward Snowden that NSA is monitoring innocent civilians all over the world being spread by media for months, it's understandable that the BOUNDLESSINFORMANT charts were seen as evidence for American spying on European countries. Glenn Greenwald presented them in that way to major European newspapers and supported his interpretation by a FAQ document saying that this tool shows "How many records (and what type) are collected against a particular country".
But now that it has become clear this interpretation was false, it also reveals that Greenwald apparently relied solely on these few documents, and was unaware of what the charts really show. I think we have to assume that Snowden also had no idea about their factual context, let alone any experience with the program - if he had, it would be even worse.
The whole story about BOUNDLESSINFORMANT not only backfired upon Snowden and Greenwald, but also upon several European governments, for example the Spanish and the French ones, who fiercly protested against the alleged US spying on their countries, and of course the Dutch one, where interior minister Plasterk was almost forced to resign because of the misinterpretation of the BOUNDLESSINFORMANT chart.
Update:
In July 2017, a Dutch journalist involved with the Snowden revelations said on Twitter that the 1,8 million records represent some 12 million pieces of metadata (which means one record consists of at least 6 fields) and that the Dutch Ministry of Defence had confirmed that they were collected from Somalia.
Links and Sources
- Le Monde/BugBrother: La NSA n’espionne pas tant la France que ça
- DeCorrespondent.nl: Cees Wiebes over de internationale gevolgen van Plasterkgate
- Jan Dirk Snel: De Tweede Kamer heeft zelf boter op het hoofd – Over de zogenaamde affaire-Plasterk
- NetKwesties.nl: Onjuiste geheimhouding regering over AIVD/MIVD
- Cyberwar.nl: Broken oversight & the 1.8M PSTN records collected by the Dutch National Sigint Organization
- DutchNews.nl: The Netherlands, not USA, gathered info from 1.8 million phone calls
- NRC.nl: NSA hielp Nederland met onderzoek naar herkomst 1,8 miljoen
- Defensie.nl: MIVD: Interceptie van telecommunicatie
- VoiceOfRussia.com: Denmark admits to tapping phones in conflict zones abroad
A Perspective on the new Dutch Intelligence Law
Since the Snowden-revelations, several countries adopted new laws governing their (signals) intelligence agencies, but instead of restricting the collection capabilities, they rather expand them. Previously we examined the new laws that have recently been implemented in France. This time we will take a look at the Netherlands, where a new law for its two secret services is now being discussed by the parliament.
The situation in the Netherlands is different in at least two major aspects from many other countries. First, there is no institutional separation between domestic security and foreign intelligence as the two secret services combine both tasks. Second, the current law restricts bulk or untargeted collection to wireless communications only, so cable access is only allowed for targeted and individualized interception.

The headquarters of the General Intelligence and Security Service AIVD
in Zoetermeer, not far from The Hague
(photo: NOS)
Secret services
In the Netherlands, there are two secret services, which were both created during a major reorganisation in 2002:
- General Intelligence and Security Service (Dutch: Algemene Inlichtingen- en Veiligheidsdienst, or AIVD), which falls under the Interior Ministry and is mainly responsible for domestic security issues, but also has a small branch that gathers intelligence information from and about foreign countries. In 2015, AIVD had over 1300 employees and a budget of 213 million euros.
- Military Intelligence and Security Service (Dutch: Militaire Inlichtingen- en Veiligheidsdienst, or MIVD), which falls under the Defence Ministry and is mainly responsible for military intelligence related to peacekeeping missions and military operations overseas. They also have to provide security for the armed forces. In 2015, MIVD had over 800 employees and a budget of approximately 85 million euros.
The Netherlands has no separate signals intelligence agency, but in 2014, the Joint Sigint Cyber Unit (JSCU) was created as a joint venture of AIVD and MIVD. The JSCU integrates the collection of signals intelligence and cyber defense operations on behalf of both agencies. The unit is located in the AIVD headquarters building in Zoetermeer and has a workforce of some 350 people.
The head of JSCU is also the point-of-contact for foreign signals intelligence agencies, like NSA and GCHQ. The JSCU operates two listening stations: a relatively large satellite intercept station near the northern village of Burum, and a very capable High Frequency (HF) radio listening post in Eibergen near the German border.
The fact that the Dutch secret services combine both domestic security and foreign intelligence tasks, also means that there's just one legal framework for both, and that authorisations are not only required for domestic operations, but also for foreign ones. Therefore, the Dutch services don't have to separate foreign and domestic communications, which proved to be such a painful job for NSA and the German BND.

The headquarters of the Military Intelligence and Security Service MIVD
at the compound of the Frederik Barracks in The Hague






































 Politie Kerkrade Limburg Netherlands, You know Which Police Officers were involved in the torturing of an innocent citezen on 13th may in the Hospital in Heerlen City. Police Database Numbers from the Centrale Phone Call: Bel OvD-OC Piket - Conflict- en Crisisbeheersing 1033190
Politie Kerkrade Limburg Netherlands, You know Which Police Officers were involved in the torturing of an innocent citezen on 13th may in the Hospital in Heerlen City. Police Database Numbers from the Centrale Phone Call: Bel OvD-OC Piket - Conflict- en Crisisbeheersing 1033190  Witness of the wounds and bruises after the torturing done by cops and Hells Angels on 13th May 2017. Untill this day you don't want to testify, you didn't want to take pictures also, You said it was better to forget that it all happen. Well guess what. We are Anonymous. We do not forgive. We do not forget.
You have seen the wounds from the Targeted individuel and we demand you to testify to the police that you have seen that he was beaten down. his head was wounded with blood, his legs were open wounded and his hands were burned from the torturing and you Bjorn Jegers you saw it. and you may not lie as Lawyer and you must know that. Don't you? or are you bribed by the Hellls Angels to? or scared for represailes. Like the Cop whoems car got bombed. Is that the reason we must be silence and let us take our life away? NO WE WILL NOT BE SILENCED ANYMORE. GOVERNMENT IT IS TIME TO DO SOMETHING!
Witness of the wounds and bruises after the torturing done by cops and Hells Angels on 13th May 2017. Untill this day you don't want to testify, you didn't want to take pictures also, You said it was better to forget that it all happen. Well guess what. We are Anonymous. We do not forgive. We do not forget.
You have seen the wounds from the Targeted individuel and we demand you to testify to the police that you have seen that he was beaten down. his head was wounded with blood, his legs were open wounded and his hands were burned from the torturing and you Bjorn Jegers you saw it. and you may not lie as Lawyer and you must know that. Don't you? or are you bribed by the Hellls Angels to? or scared for represailes. Like the Cop whoems car got bombed. Is that the reason we must be silence and let us take our life away? NO WE WILL NOT BE SILENCED ANYMORE. GOVERNMENT IT IS TIME TO DO SOMETHING!  Second witness who saw the wounds of the Targeted Individual after the torturing. Also kept in silence and said noting to the cops, KVK 14109164. BTW NL12345678
Second witness who saw the wounds of the Targeted Individual after the torturing. Also kept in silence and said noting to the cops, KVK 14109164. BTW NL12345678





